 |
| Security Guides for IBM Cloud |
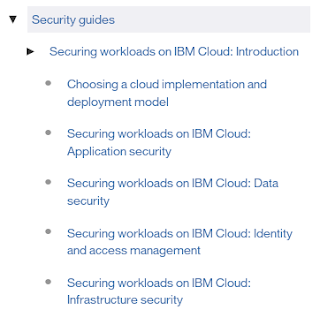
The guide "Securing workloads on IBM Cloud: Introduction" is closely aligned with the security-related Architecture Blueprints for Cloud. The guide right now has the following sections:
- Application Security takes a 360 degree look at applications and what needs to be considered to secure them, ranging from the application container over network to identity management.
- Data Security digs into different kind of data storage and the technologies to encrypt data and keep the integrity.
- Identity and Access Management covers approaches and technologies on how to securely keep tabs of different roles like administrators, developers and users. It starts with bringing them into the system environment to auditing their actions.
- Infrastructure Security gives great insight for a guy like me into lower layers like firewalls, gateways, VPN, DNS managemen and more. It helps to understand what is happening behind the curtain in the IBM Bluemix / SoftLayer data center.
- Physical Security goes even deeper to buildings and material. Flood protection? Heating and cooling? Perimeter control? All covered.
- Secure DevOps has an overview of secure engineering practices, security functions and controls including ISO and NIST standards, vulnerability and incident management and operation controls.
- Security Information and Event Management (SIEM) gives a concise introduction into logging, access trails and event management.
- Security Policy, Governance, Risk and Compliance concludes the guide with an introduction into how security policies and risks can be managed or governed, and how this ties in with standards (compliance).
Good reading and enjoy the weekend!